Introduction
The Cybersecurity Maturity Model Certification (CMMC) program was developed by the Department of Defense (DoD) as a program to clearly define standards for cyber protections for companies in the defense industrial base (DIB). It is meant to enable DIB companies to meet evolving threats and to safeguard information supporting DoD projects and persons.
On November 4, 2021, CMMC 2.0 was released. It includes many important structural changes to the CMMC framework. The changes are intended to simplify and alleviate complexity and implementation costs, especially for small and medium-sized businesses relative to the original CMMC 1.0 framework. In addition, other significant changes were made to refine both the content and the process for implementing CMMC 2.0.
This article will cover the areas described above and will also include how these changes may affect our clients, and the timeline for implementing CMMC requirements.
What is CMMC 2.0?
On November 30, 2020, “Defense Federal Acquisition Regulation Supplement: Assessing Contractor Implementation of Cybersecurity Requirements (DFARS Case 2019-D041)” went into effect. This interim DFARS rule introduced CMMC 1.0 requirements for DoD contractors and subcontractors.
In March 2021, the DoD started an internal assessment of the CMMC program’s implementation to refine the policy and program implementation. This review resulted in “CMMC 2.0” which updates the requirements and program structure and to improve and streamline implementation of the program.
Results from this review process
- Changes in the framework will follow the rulemaking process in accordance with title 32, and title 48 of the Code of Federal Regulations (CFR). The rules include both a public comment period and congressional review. Following the rulemaking process is estimated to require between nine (9) and 24 months to complete.
- In CMMC 2.0, the framework has been reduced from five levels to three levels.
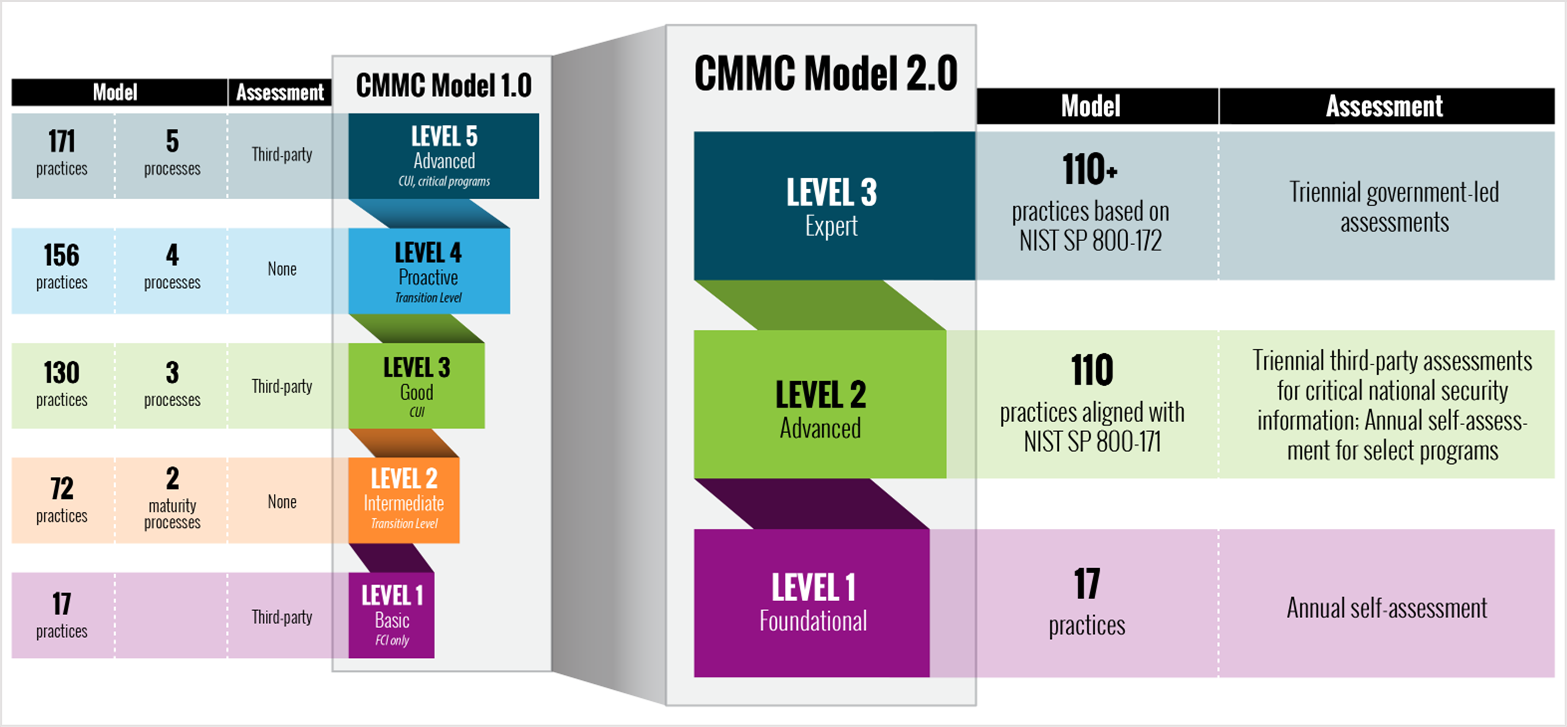
Graphic of CMMC Model 1.0 & CMMC Model 2.0 Comparison (OUSD A&S – Cybersecurity Maturity Model Certification (CMMC) (osd.mil))
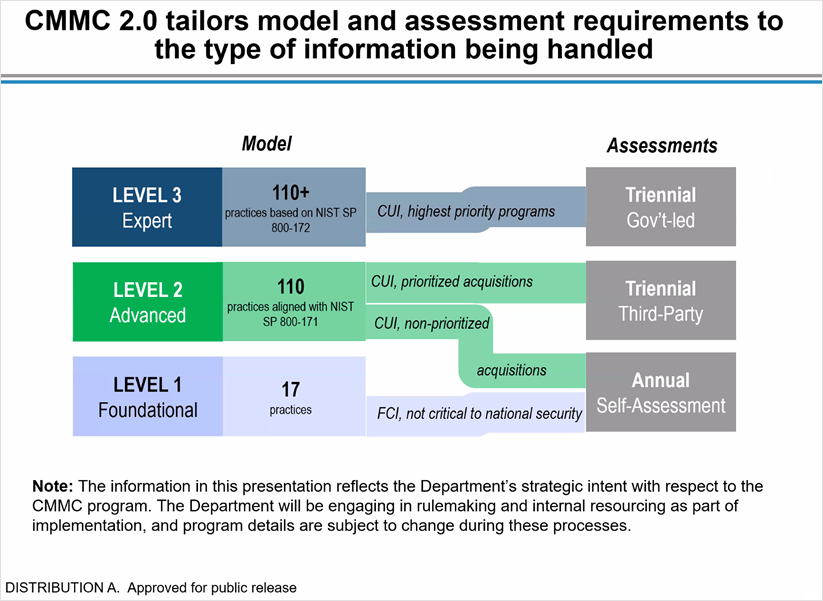
- Allowing CMMC Level 1 (Foundational) to be achieved through annual self-assessments and annual affirmation by DIB company (C-level) leadership.
- Bifurcating Level 2 (Advanced, formerly Level 3) to identify prioritized/weighted acquisition requirements that will require triennial independent assessments. Non-prioritized acquisitions will require annual self-assessment, along with annual company affirmation.
From CMMC Accreditation Body (CMMCAB) “CMMC 2.0 Discussion Town Hall”
- CMMC Level 3 (Expert) will be assessed triennially by government officials
- The new process will allow DIB companies the use of time-bound (potentially 180 days) Plans of Action & Milestones (POA&M)
- This means that all non-prioritized CMMC requirements do not initially need to be met in order to be awarded a contract. Shortcomings would need to be addressed by the POA&M within a strict time frame.
- POA&Ms will not be allowed for highest weighted requirements
- Additionally, waivers will be allowed on a very limited basis and will require senior DoD approval to minimize potential misuse of waivers
Why were these changes to the CMMC framework made?
- Simplify CMMC and provide greater clarity on cybersecurity regulatory, policy, and contracting requirements
- Simplifying the model from five levels to three
- Allowing self-attestation and company-level self-affirmation for Level 1 compliance
- For non-prioritized acquisition, allowing self-attestation and company-level self-affirmation for Level 2 compliance
- CMMC requirements now align with existing governmental guidance provided by NIST 800-171 and NIST 800‑172 standards and other recognized security guidelines
- Eliminating CMMC-specific requirements that had been included in CMMC 1.0
- Focusing third-party assessment requirements on companies involved in the highest priority programs
- This is done largely by implementing the self-attestation and self-affirmation processes described above
- Increasing Department oversight of professional and ethical standards in the assessment ecosystem
- In March 2021, a Memorandum of Understanding (MOU) between the Office of the Under Secretary of Defense for Acquisition and Sustainment, and the CMMC Accreditation Body (CMMC-AB) was signed.
Included in this agreement, the CMMC-AB is to:- Achieve and maintain ISO /IEC 17020 certification.
- Achieve and maintain the ISO / IEC 17011 certification
- Require CMMC Level 3 certification for all internal systems and networks
- Conform to DoD standards for personnel and outsourced and other managed services
- In March 2021, a Memorandum of Understanding (MOU) between the Office of the Under Secretary of Defense for Acquisition and Sustainment, and the CMMC Accreditation Body (CMMC-AB) was signed.
CMMC rollout and contractual requirements and timeline
The interim DFARS rule for CMMC (1.0), effective November 30, 2020, had a five-year phase-in period. During that time CMMC compliance is only required in select contracts. The DoD isn’t planning to include CMMC requirements in any contract prior to the CMMC 2.0 completion of the rulemaking process (https://www.acq.osd.mil/cmmc/about-us.html). After completion of the rulemaking process the CMMC framework will be implemented according to regulatory requirements.
The rulemaking process is estimated to have a 9-to-24-month timeline.
How will these changes affect PROCAS clients that are DoD contractors?
A large percentage of our clients who are DoD contractors will benefit significantly from these changes in CMMC 2.0. The costs for meeting CMMC 2.0 requirements for Level 1, and many companies requiring (non-prioritized) Level 2 certification are projected to be significantly lower. This is largely due to the removal of the requirement to be assessed by a CMMC-AB certified assessor/assessor organization.
This is not to say that there will be no costs or other concerns in this process. Due to the specialized knowledge required to understand the cybersecurity requirements encompassed by CMMC, many companies may find it useful to utilize the services of consultants or other advisors who are familiar with NIST 800-171 and/or NIST 800-172 to assist them in the self-assessment process.
Also, it is important to be aware that the self-assessment, and self-affirmation (by C-level executives) is also accompanied by the DoD seeking to more rigorously enforce oversite and penalties for entities that do not meet the standards that they affirm to be in compliance with. This makes a strong case for getting expert advice on how to move forward in meeting the requirements for CMMC 2.0.
PROCAS’s Software as a Service (SaaS) is audited at least annually against the American Institute of Certified Public Accountants’ (AICPA) Service Organization Controls (SOC) reporting framework for Security & Availability by independent third-party auditors. Our audit is expanded to also include CMMC requirements as published at the time of the audit so that we will be more prepared once the rule making process is complete, the framework is finalized, and companies can be CMMC certified by third parties.